The WP-Invoice plugin from Usability Dynamics, Inc. contains several security vulnerabilities. The wordpress.org stats claim there are 5,000+ active installs, so this is not a highly used plugin but anything that is related to billing/invoices always puts me on edge. If you use this plugin I encourage you to update immediately.
I only evaluated the free version of this plugin and did not look at any of their paid add-ons for vulnerabilities. I discovered three issues that were accessible to unauthenticated users and one issue that required a valid WordPress account.
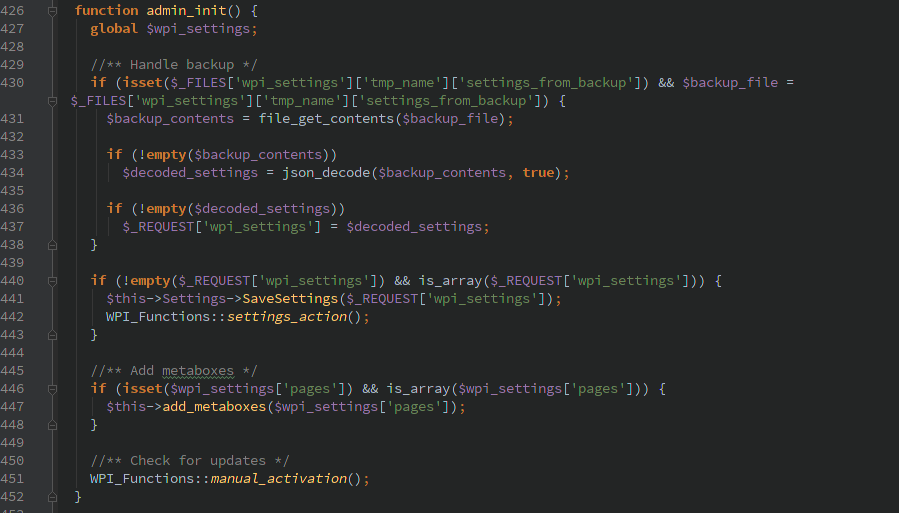
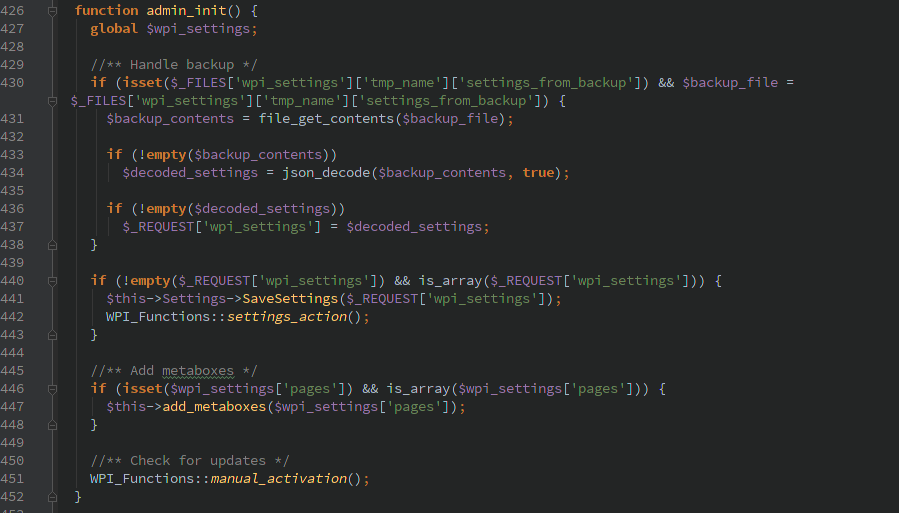
Unauthorized Setting Changes
Inside class_core.php the function admin_init() gets hooked to the ‘admin_init’ WordPress action which is called when the admin files are loaded, not just when an account with administrator access is used.
Inside this function it takes user input and without verification updates the sites settings. This merges in the existing settings so by passing individual settings only those can be updated. This allows changing settings like the emailed templates, paypal email address, and various other scary parts.
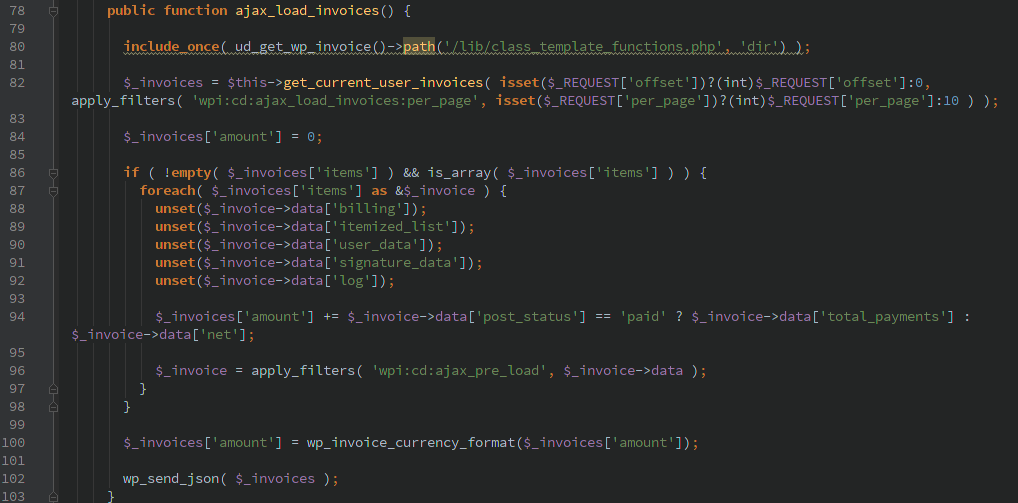
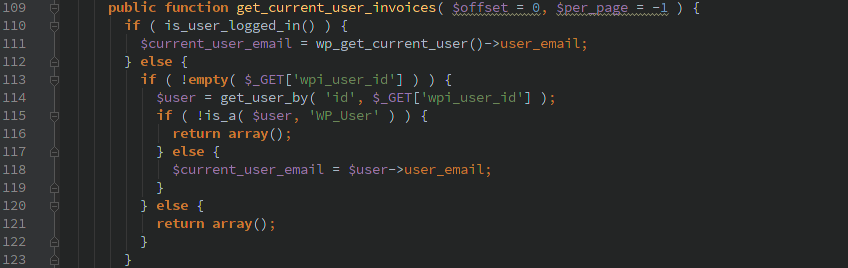
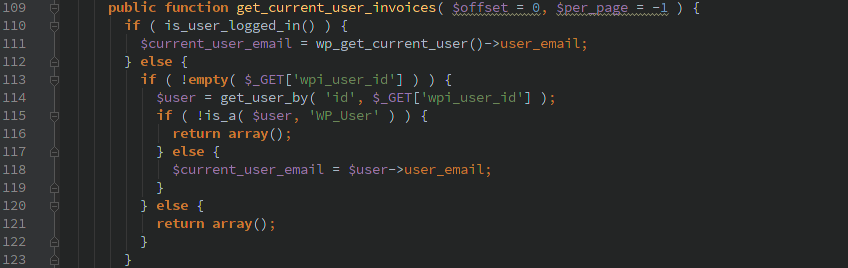
Retrieving invoices of arbitrary users
I’m not sure this is the most critical of the flaws, but it does allow release of sensitive data and the invoice numbers can be used in the next vulnerability.
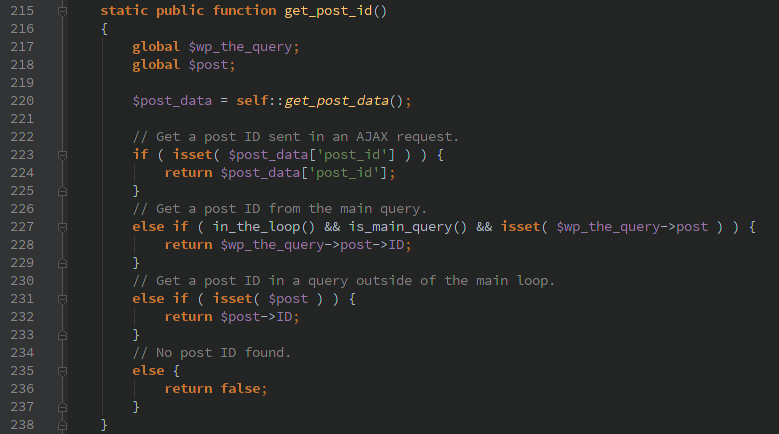
Here we have AJAX actions registered for logged in and not logged in users.
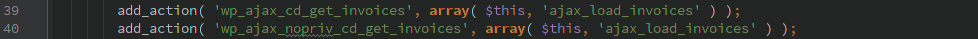
Upon first glance I thought this would allow only the current users invoices to be loaded.
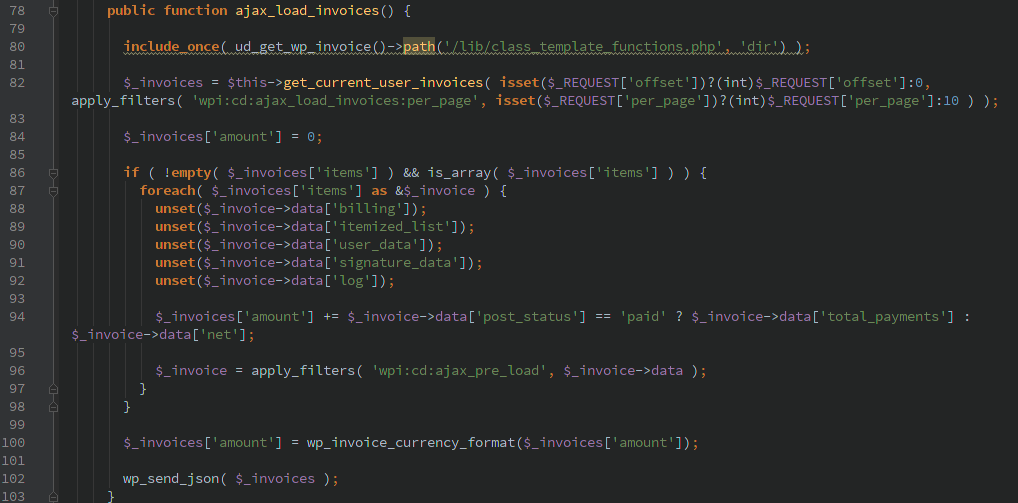
Upon further examination if the user is logged in then their invoice will be loaded, but if the user is not logged in $_GET[‘wpi_user_id’] can be passed containing a WordPress numeric user_id.
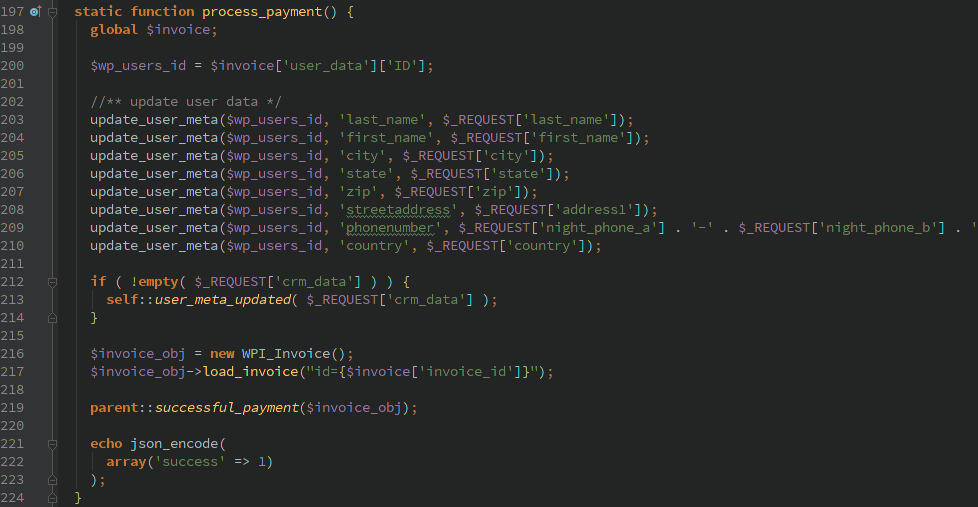
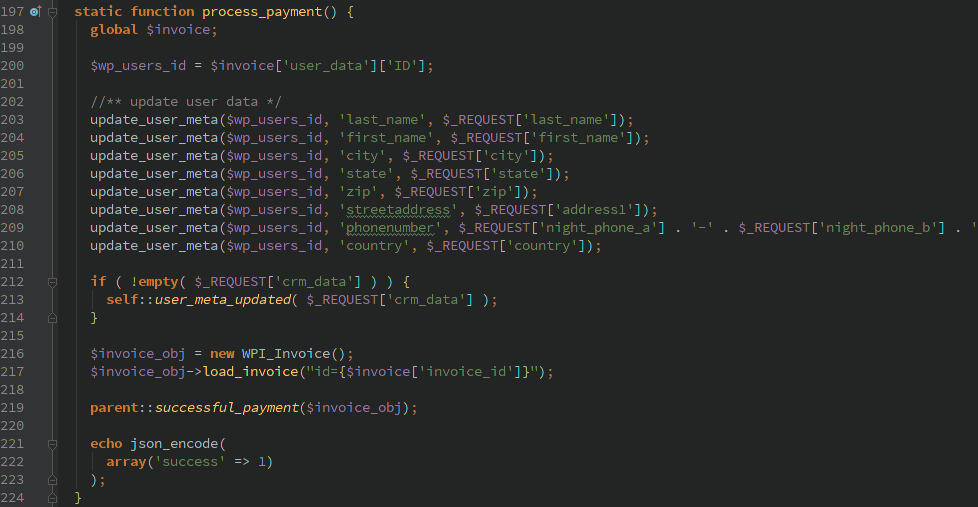
Updating previously invoiced users meta data
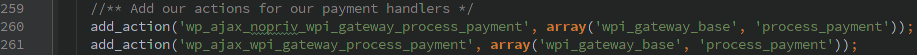
Through the magic of unauthenticated AJAX the ‘wpi_gateway_process_payment’ actions can be called.
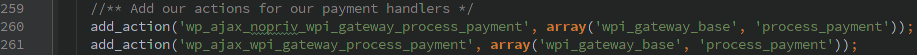
The wpi_gateway_base::process_payment() function takes user input in order to call the process_payment() function in various payment gateway handlers.
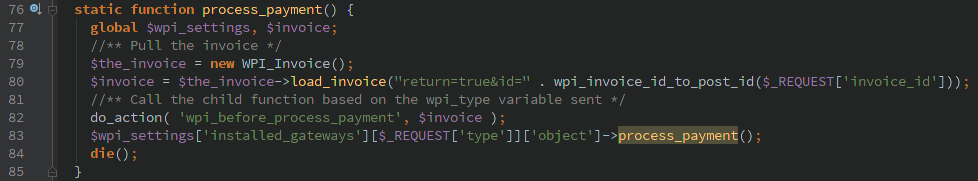
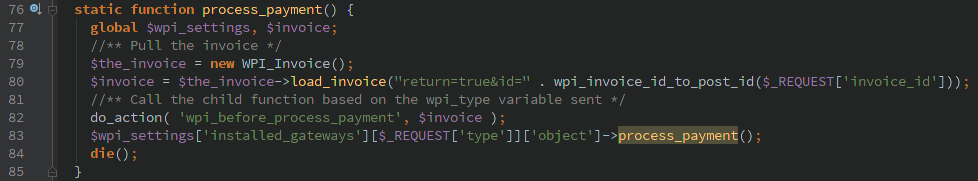
In this case the ‘wpi_paypal’, ‘wpi_interkassa’, and ‘wpi_twocheckout’ all allow this to happen. Below I’ll only show the ‘wpi_paypal’ variation. This allows various type of the users meta data to be updated and if their CRM plugin is installed any of the attributes that are used in there can be updated.
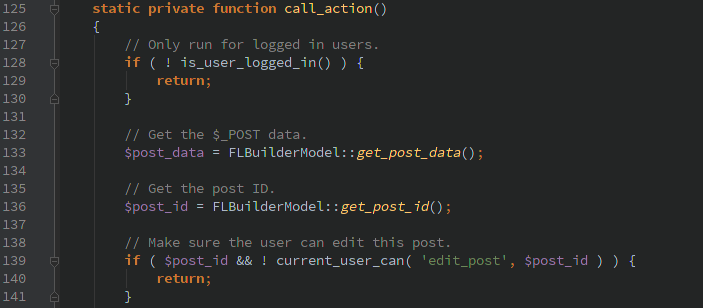
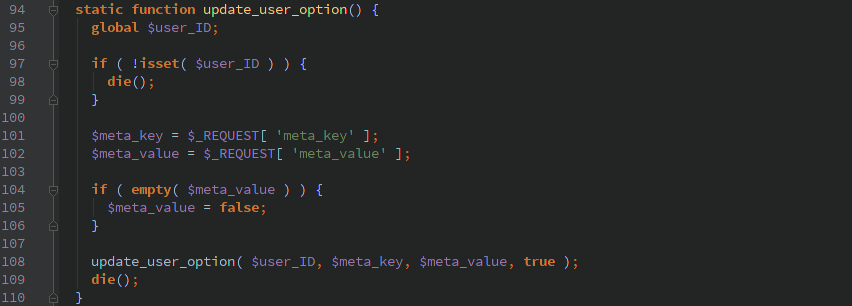
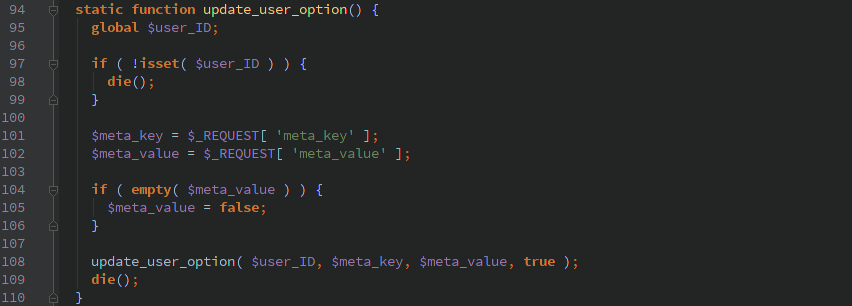
Privilege escalation of logged in users
Through the ‘wpi_update_user_option’ AJAX action, a logged in user can pass arbitrary ‘meta_key’ and ‘meta_value’ that gets updated for their account. Many of these options are accessible to the user via their profile, but typically a user should not be able to modify their ‘wp_capabilities’ or other potentially dangerous fields.
Timeline
- 1/15/2016 11:28am Initial contact email sent
- 1/18/2016 3:14am Contact information received
- 1/19/2016 11:58am Full disclosure email sent
- 1/29/2016 6:23am Vendor responded saying issues were resolved in latest release